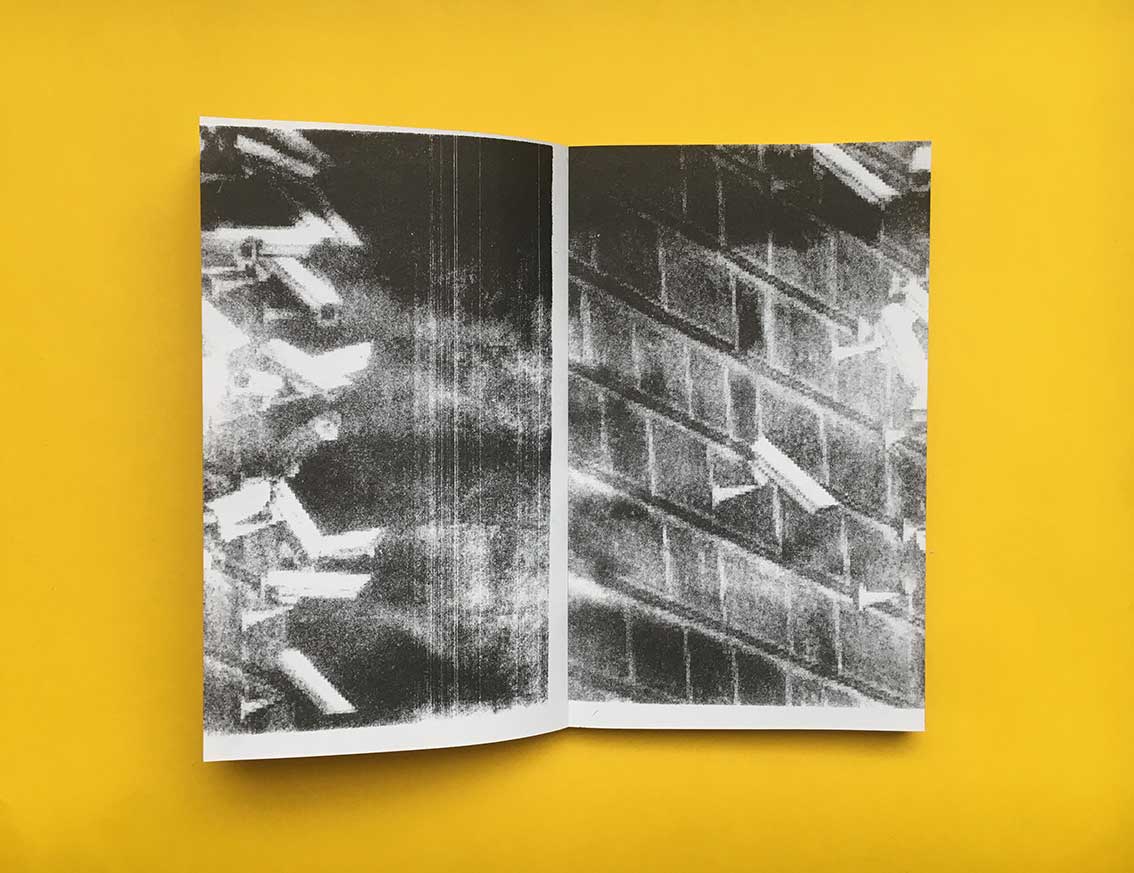
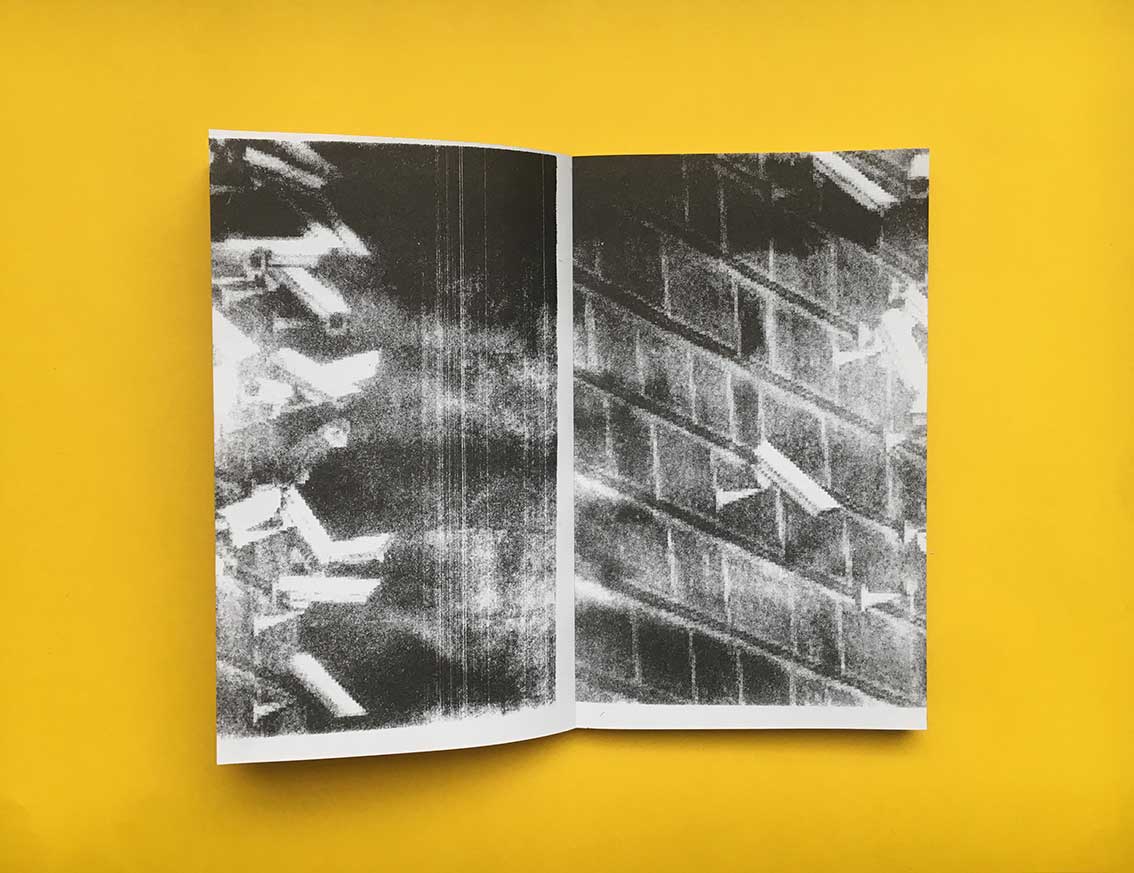
Everything You Have Ever Clicked on Can And Will Be Used Against You.
— 2018
Our daily relationship with our screens is changing as we are tagged,
tracked, our behavior predicted and sold. What role can the artist play
in the setting and how can he or she position himself or herself in a
future surveillance scenario? “I have nothing to hide, I'm not a terrorist.”
“I have nothing to hide, it’s okay if the NSA spies on me", “I am doing
nothing wrong or illegal, so why bother?”
George Orwell's 1984 movie
opens with Winston Smith carving out a pocket of privacy by crouching
in a corner of his apartment where the telescreen-and thus Big Brother
can't see and writing a diary entry. These days, that Stalin-inspired nightmare
seems to be real. In June 2013 Edward Snowden gave The Washington post
and The Guardian secret documents about spying activities done by the NSA.
He declared that the NSA was guarding and scanning online documentation worldwide and how the NSA had decoded internet communication. Snowden was a former CIA employee and system administrator for the NSA.
According to Alice Twemlow who is the co-founder and chair of a Design Criticism
program at the School of Visual Arts in New York: “The way in which new
media technologies are used by the state and corporations to compile our
personal data has emerged to the issue-du-jour of the global design
community” There is more than only thinking that the NSA is monitoring
us. At On the surface, we are talking about data dealing, privacy, algorithms,
the privacy paradox and about how the relationship with our screen is
changing, but it goes much deeper than that. What is the value of privacy?
What happens when our privacy rights are being taken away from us? Has
our behavior changed due to the Snowden revelations and what can we
say about the future of mass surveillance? Media theorist Geert Lovink
writes: “The value of the internet generation has been dashed to pieces: decentralization, peer-to-peer, rhizomes and networks. Everything youhave ever clicked on can and will be used against you”